Southwest Research Institute (SwRI) has developed an intrusion detection system (IDS) to protect ground vehicles against cyberthreats to embedded systems and connected vehicle networks. While developed for military vehicles, the system can also be used to scan for anomalies in passenger cars and commercial vehicles.
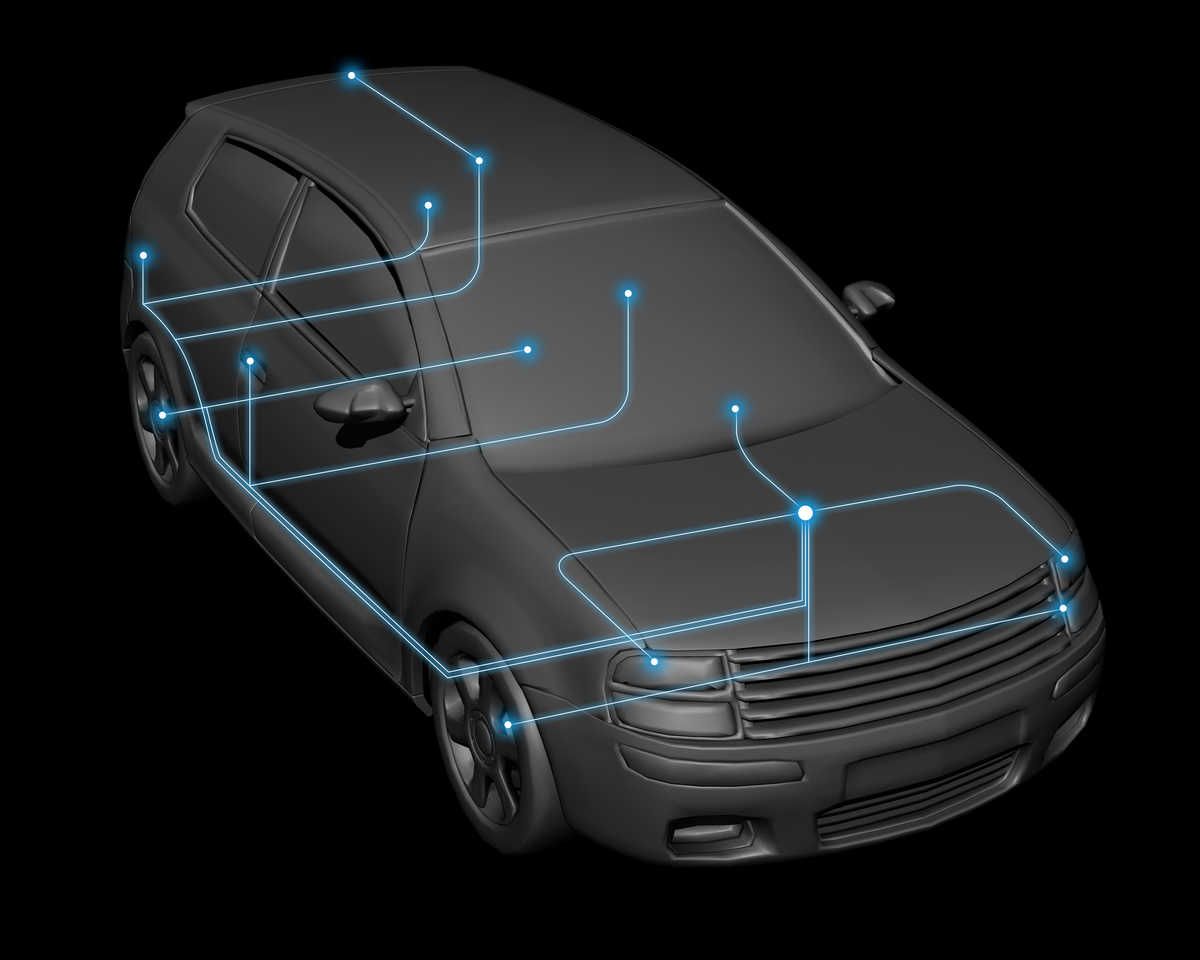
The IDS technology, developed by SwRI in collaboration with the US Army Ground Vehicle Systems Center (GVSC) Ground System Cyber Engineering (GSCE), uses digital fingerprinting and algorithms to identify anomalies in communications across automotive systems and components. Military, passenger and commercial vehicles use the standard Controller Area Network (CAN) bus protocol to enable communications across various nodes or electronic control units (ECUs).
The CAN protocol, for example, informs a dashboard display when a sensor detects low oil pressure or when headlights have been activated. It also relays operational communications for systems such as the transmission and other critical automotive technology.
“A cyberattack could potentially send erroneous information across the CAN protocol to alter or impede a vehicle’s operations,” says Jonathan Wolford, an SwRI engineer who co-authored a paper on the subject. “An attack on several connected vehicles could have disastrous effects.”
Since 1986, CAN has been a standard automotive protocol, providing a reliable and flexible platform to transmit information. However, it was not designed with cybersecurity protections. As modern vehicles become increasingly connected via external networks, the CAN system is increasingly vulnerable to potential cyberattacks, particularly from bad actors sending false messages.
SwRI’s new algorithms digitally fingerprint messages on nodes that transmit information via the CAN bus protocol. Digital fingerprinting allows SwRI’s intrusion detection systems to identify when an unknown/invalid node or computer is connected to the vehicle network. These algorithms use the CAN transceiver’s message transmission to track low-level physical layer characteristics — such as the minimum and maximum voltages as well as the voltage transition rates for each CAN frame — to create these digital fingerprints.
The researchers trained the system with baseline data to build a fingerprint of each node, to understand characteristics and better identify anomalies. With digital fingerprinting, the intrusion system accurately identifies messages sent from unauthorized nodes or when a valid node is sending spurious messages, indicative of a “masquerade attack.”
After training the system, SwRI engineers injected false data, and the algorithms flagged them instantly. The system is capable of both identifying threats and defending against them.
“These attacks are theoretically easier for bad actors who have physical access to a vehicle, but vehicles are also vulnerable from wireless attacks,” said Peter Moldenhauer, an SwRI engineer who co-authored the research. “Our system is designed to build cyber resiliency into the CAN protocol as we move to more connected and automated vehicle networks.”





